During the 1980s, in countries of Western Europe and the United States home computers such as the Apple II, the ZX Spectrum or the Commodore 64 became affordable symbols of technological modernity. The mass dissemination of home computers, named microcomputers or just micros, which were supposed to be used primarily by teenagers for educational purposes, had an impact on the development of the information society.1 A smiling teenager sitting next to his micro with a running edutainment program became the omnipresent symbol of things to come.2 This popular image was one major growth factor in the demand for home computers.3 Parents who wanted to secure a prosperous future for their children were easily convinced that they should purchase a micro rather sooner than later.
However, there was also a downside to mass computerization. In the 1980s, a different picture of the smiling teenager sitting by his computer began to emerge – that of a hacker who uses his knowledge of information technologies to conduct felonies such as credit card fraud, and causes irreversible damage to computer networks.4 The media image of teenage hackers was influenced by moral panic about adolescents engaged in subcultures and drug abuse.5 The emergence of new forms of social and cultural practices among young computer owners who spent days and nights in front of their micros alienated them from their parents. In media discourse, the hacker was alone, interacted only with information technology artifacts, and lacked social relations.6
Contrary to the media image of hackers, their subculture was based not merely on the interaction with computers, but also on complex interactions with other computer users who shared the same approach to the new technology as well as the respective social customs. Their activities were far less spectacular than the movie War Games (1983) depicted. Actual hackers were not extraordinary computer geniuses, but rather ordinary adolescents with programming skills who massively copied computer games. The omnipresent term hacker was scarcely used by adolescents; they rather appropriated terms such as computer underground, computer scene, or just the scene for insiders as synonyms. To understand the activity of this subculture, we need to scrutinize not only the relationship between human beings and technology, but also the context of popular culture and other subcultures of the era, which greatly influenced the shape of teenage computer underground.
2![]()
While discussing this computer underground, I will refer primarily to academic literature on the social shaping of information and communication technologies (ICT). Moreover, I will refer to monographs on other subcultures from the era. This approach helps to understand the specific nature of the computer underground, which includes relationships of users with their micros, as described in depth by Sherry Turkle,7 as well as social interactions among users within the framework of their subculture group. Despite the huge popularity of the scene in the 1980s among computer users, it has been completely omitted in current monographs on cybercultures.8 These monographs propose a deterministic approach to the technology. The internet is frequently described as a technology that significantly influenced new forms of social activities among ICT users. For instance, as the archetype of cyberculture David Bell has proposed Multi User Domain (MUD), an early internet fantasy multiplayer game, completely ignoring not only the mass computer underground, but also the Bulletin Board System (BBS) culture of the 1980s.9
My article discusses the cracking scene – as one of numerous subcultures that arose in Northwestern Europe in the 1980s. For crackers, adolescent males with mostly middle class background, home computers became subcultural artifacts. Practices of using them became a form of creating social distinction in a peer group. The focus is on the process surrounding the appropriation of the home computer from popular consumer electronics to a subcultural artifact. I will also discuss the process of developing teenage masculinity by participating in cracking scene rituals.
The growth of the scene in the early 1980s took place in Northwestern Europe: West Germany, the Benelux countries, the UK and the Scandinavian countries. Many of the cracking scene activities were based on transnational contacts between crackers; thus the best way to grasp its scope is to discuss it as a European, not a national phenomenon. In this region, the growth of the scene was linked to the mass dissemination of relatively affordable home computers in middle class households. American subcultures of young computer users vary because of several differences in available technologies as well as users’ cultural background.10
3![]()
I focus on the 1980s – the decade of the establishment, quick expansion and subsequent decline of the mass cracking scene. Due to technological and cultural changes, the practices of game cracking during the 1980s and the cultural practices of the 1990s computer subcultures differed. My article is based primarily on contemporary sources such as numerous scene magazines, software artifacts and interviews with members of the scene.
Historical scholarship has perceived the development of youth cultures in postwar Western Europe mainly as the growth of socially and politically active youth movements, for instance peace and environmental protection movements.11 On the other hand, scholars of British cultural studies focus on the different milieus of working-class subcultures such as punks and skinheads to describe the cultural practices of working-class youth without a strong or explicit political engagement.12 In the late 1990s and the 2000s, however, scholars became interested in different forms of European and American youth cultures.13 Especially the decade of the 1980s is regarded as a flourishing epoch of new forms of youth culture, for instance the graffiti scene, bodybuilding culture, goths, hip hop culture, the blitz kids, metalheads, poppers, the rave and acid scene, and skateboard culture. My article contributes to the growing body of work on the diversity of youth lifestyles in 1980s Europe by highlighting how computer users established social and cultural practices with features similar to other forms of youth subcultures in this era.
1. From Gaming Culture to Computer Underground
Home computers such as the ZX Spectrum, the Commodore 64, the Atari XE or the BBC Micro became huge successes of the early 1980s. These hardware platforms could be used for home entertainment as successors to game consoles like the Atari 2600, which was introduced in the late 1970s. Console games were offered only on expensive ROM cartridges, which could not be copied at home. Home computers as mass memory storage used disk drives or, even more popular, ordinary tape cassettes. Thus, it was easy to enlarge one’s own game collection by visiting a friend and copying games from his disks or cassettes. The easiness of accumulating considerable games collections for free is one of the neglected factors in the 1980s home computer boom. British researchers of this boom have primarily pointed out schools as sites of frequent exchange of copied software.14 An insider of the computer underground remembers such practices: ‘Games were traded over tapes and floppies in school, in the soccer fields and homes of millions of teenagers. In 1985, you could walk into any school in the Western world and find kids with long lists of games they were swapping with each other. […] “I have these games” – “which do you have?” was the common conversation over the lunch-hour (Please note you never talked about games in singular – you always traded in plural).’15
4![]()
Home computers could be used exclusively for gaming. With an implemented compiler of the entry level BASIC language, however, a user could write his or her own programs and learn how to control such an advanced technological device. Programming techniques could be easily learned with the help of several entry-level programming textbooks and courses in computer magazines. This aspect of the appropriation of home computers is described in depth by Sherry Turkle with the metaphor of the computer as the second self.16 Micros were also used by teenagers in a way unpredicted by the computer industry and parents. Computers became artifacts that presented adolescent male users a new form of self-expression by offering the possibility of being ‘inside subculture’, to use David Muggleton’s phrase.17
The popularity of game copying among peers was obviously not welcomed by software companies. They influenced popular computer magazines, such as the English Computer and Video Games and Zzap!64, to launch media campaigns to convince computer users that copying games was unethical and in fact a crime.18 Software companies also introduced copy protection in the games they sold. A copy of such a protected program simply crashed during the attempt to start it.19 It cannot be gauged if this policy really decreased the popularity of copying games. However, there was a side effect to the software companies’ policy. By advertising that copying one’s favorite games for a friend was a crime, the attractiveness of such practices greatly increased. Anyone with a little programming knowledge was able to remove copy protections. Most gamesters were male adolescents, and such practices fit perfectly into the teenage struggle for masculinity in a peer group. The policy of software companies and anti-piracy campaigns in computer magazines induced a part of the everyday lives of adolescent computer users to evolve into computer underground.
Two subcultures that thrived in the 1980s share features with computer underground: the graffiti scene and club culture. Writing illegal graffiti in urban spaces and evading the police was one of the challenges of being a graffiti writer.20 The same idea of illegality was popular among British clubbers.21 Those who attended so called ‘underground’ parties distanced themselves from common disco-goers who attended ‘mainstream’ discos. The same momentum of gaining distinction from ‘ordinary’ computer users was one of the most significant traits of the cracking scene. Practices of copy protection removal and the distribution of games became an art for art’s sake. As Levy put it in 1984, ‘defeating the fascist goon copy-protect was a sacred calling, and would be lots of fun’.22 A British teenager explains: ‘I must admit, I do have great fun trying to crack protection systems. But that’s more to do with the fun of it, rather than anything to do with the programme once you’ve got it on tape.’23
5![]()
Media coverage of the purported abuse of information technology by adolescents shaped the early 1980s as the period of hacker peril.24 Teenage hackers were accused of breaking into the networks of commercial companies and military agencies as well as committing massive credit card frauds. This media peril was exploited by Hollywood with the movie War Games, which became popular among teenagers.25 Leslie Haddon describes the impact of hacker moral panic on micro users: ‘One interviewee, for example, even tried to reenact the earlier role of the “hacker” in small ways, such as programming in solitude in the evening. In this endeavour, the current equivalent of the challenge of breaking into telecommunications systems had become breaking into protected software.’26
The relatively easy practice of software copy protection removal became a popular equivalent of the Whiz Kids felonies, covered and exaggerated by the media. Levy quoted the terms defying, breaking and cracking that were originally used to describe the removal of copy protection.27 The latter term became the most popular, as young users referred to themselves primarily as crackers. The term cracking scene was adopted as a popular description of the subculture of software pirates. However, terms like illegal scene, pirate scene and computer underground were widely used as synonyms.
During the first half of the 1980s, young programmers able to crack copy protection and copy games started adding their own signature to copied software. It became customary to add the phrase ‘cracked by…’ and the author’s nickname to the game’s title screen.28 Simple signatures, similar to graffiti tags, evolved into independent crack screens or crack intros, where instead of the basic signature made with standard computer font, the name of the cracker was displayed as a well-designed full screen color logo. Later, such logo screens were enriched with animations, music, long statements and greetings displayed at the bottom of the screen.
6![]()
Crack screen of Berlin Cracking Service, 1984
(http://www.atlantis-prophecy.org/recollection/?load=online_issues&issue=0&sub=article&id=2)
Becoming a cracker frequently began with having access to pirate computer games provided with crack intros. Young users were impressed by the fact that their peers could crack and modify games, and if they had some experience with programming, they thought about becoming a cracker themselves. Here is the memory of a German cracker with the pseudonym ‘Weasel’: ‘I started […] with copying games from school mates and other friends who also had a C-64. […] Another thing I always was interested in were those great intros from all the groups […] who cracked those games I copied into my collection. […] I was pretty amazed that there were people somewhere on the world doing highly illegal things like CRACKING games – removing the copy-protection from the original software to be able to copy it to anybody around freely without a problem. […] I once said to myself: One day I wanna be one of those guys as well.’29
The games distributed among crackers could, or even should, be copied further; however, the original crack intro was not to be removed. A crack intro with a characteristic and unique cracking group logo was a symbol of the authorship of a specific crack – analogous to the graffiti scene: if a graffito was made by a group recognized by other local groups as part of the subculture, it was not to be painted over by another group. Similarly, once added to a program, a crack intro was not to be removed, and the visual style of the logo was not to be copied and used by another group. Currently, in the prevailing discourse of the open source movement, programs distributed for free with the respective source code published can be copied and modified. However, this is not the case in the cracking scene. Rules concerning the authorship of any ingenious code and design were recognized.30
Adolescents who spread their games among school peers started establishing more remote contacts with the help of telephone numbers given in crack intros. The games were distributed via local personal networks and correspondence. Software was distributed on a non-profit basis; however, the receiver was supposed to send other pirate software to the sender.31 The most important cultural value of this activity, besides acquiring games, was its supposed illegality. Yet, some crackers claimed ideological motivations: ‘People think you are a murderer, robber or another criminal element, but what are you really? You copy games for all those poor guys whho [sic] just can’t afford to buy fuckin’ expensive original games, eh? And you crack to copy the games.’32
7![]()
In spite of such claims, the practice of cracking should rather be perceived as a form of building adolescent masculinity through supposedly illegal acts and the distribution of highly desired commodities among peers.33 It was a complex set of different reasons that made cracking attractive for adolescent males. Media moral panic about hackers made such figures widely recognized and highly esteemed by young computer users due to their supposed hacking skills. Only with some knowledge of programming could one modify computer games and commit a supposedly criminal act. In public discourse, the figure of a hacker is seen as a lonely geek who lacks social skills and interactions. But being a cracker actually required advanced social skills to establish and hold a position in a peer group.
This social aspect of cracking is one of the reasons why this subculture became so prominent primarily in Northwestern Europe. Home computers, with the biggest market hit – the Commodore 64 – were affordable for middle class households. This is why computer users were easily able to find other owners of the same computer model and could exchange software. The fact that crackers belonged to the middle class can be deduced from their everyday lives as described in the available testimonies. For instance, they lived in suburbia in relative welfare and financial security, and had high educational aspirations. However, the scene materials contain no clear statements on crackers’ social background; it was probably a form of taboo. Thornton analyzes this phenomenon in depth in the case of club cultures, where any references to the social status outside of the club life were a strict taboo.34
The dissemination of the cracking scene practices in other geographical regions was very limited. According to The C-64 Scene Database (CSDB), the scene became somewhat popular in South and Eastern Europe as well as Australia.35 The American scene, very different from the European, will be briefly discussed below. In regions with a much lower income level, home computers were luxury commodities and did not become popular enough to lead to the emergence of cracking groups. In Central Europe, a cracking scene developed only in Poland and Hungary in the early 1990s, when the introduction of the free market economy resulted in the quick rise of salaries and a decrease of computer prices.36 Another reason that the scene was geographically limited was the fact that in other regions, different hardware platforms were common, for instance clones of ZX Spectrum, Atari XE/XL or Sharp instead of the more expensive C-64. Fewer games were released for such platforms and their users did not develop sophisticated software exchange networks.
8![]()
2. Inside the Computer Underground
The rise of the cracking scene was greatly influenced by the huge success of Commodore 64 computers introduced in 1982; only the C-64 reached international popularity. Thus, C-64 users were eager to look for contacts with peers from abroad to acquire games that were domestically unavailable. Exchange networks for pirate software grew in Western Europe and the United States, where easily affordable home computers were popular among adolescents. However, the differences between distribution systems on both sides of the Atlantic were substantial. In the US, where modems were widely popular, the computer underground appropriated the Bulletin Board System (BBS). Games were uploaded and downloaded from password protected underground BBSes. In Europe, where modems were rather scarce and international calls expensive, the whole distribution of pirate games was based largely on snail mail, and BBSes spread only in the late 1980s.
Crackers not only removed copy protections. They also tried to modify and improve original games. The aim of such modifications was the removal of all noticed errors and glitches in the original code, since the cracked game was meant to be superior to the original in every possible way. Another popular practice was the compression of game files. This was important for practical reasons: it was easier to send a compressed game on one floppy disk than the original two-disk version.
As games from the 1980s were far more difficult than comparable products are today, there was another popular form of modification. There was no ‘Save’ option, hence one needed to spend an enormous amount of time finishing difficult arcade games. Crackers helped gamesters with the introduction of so called trainers, a modification of the code responsible for losing lives or energy in the game. A decent cracker could add a simple question in his crack screen: ‘Do you want unlimited lives? Y/N.’ By pressing one of those keys, the player could choose the modified or the original game version.37 Aside from modifying games, crackers also made graphics and music that was used in crack screens, or distributed independently.
9![]()
Virtually from the beginning, everyone in the computer underground used pseudonyms, or handles, instead of their real names. This custom was already introduced when the police did not yet have any interest in computer piracy. It was a cultural trait, typical for subcultures, rather than a way of concealing one’s true identity from law enforcement agencies. The basic social structure of this subculture was the scene group, which mostly encompassed a few members. It was customary to write a personal handle along with the name of the group divided by a slash.
The scene group’s function was similar to that of a graffiti crew, as discussed by Macdonald: ‘A crew is a group of likeminded writers who band together under a single name to form a union. Crews can be small or large, illegal or legal, local or even international. But they all share a common purpose – support.’38 Aside from the support offered by the group, it was easier for a team than for a single person to distribute games. One member was responsible for copy protection removal, another one made graphics and music for crack intros, and yet another member was responsible for the distribution of games.
To become involved in this subculture, one had to get in touch with current members. Writing to the address published in one of crack intros was one option, but members could also be found in the local area. ‘Weasel’ describes how his direct contact with the scene began when he noticed a teenager with a collection of diskettes while hanging around in a local skate park: ‘I started talking to that guy and asked him what disks that are and what would be on them. He was very nice and started to talk to me as well and told me about him being a musician with the handle HAVOK in a computer group called FRONTLINE on the C-64. […] he invited me to come with him to a weekly meeting of his group. […] At the following weekend I met with Havok and drove to the meeting place – a Burger King restaurant […]. I was pretty shy at the beginning so that I was only just watching all of them person by person to get some impressions about those “illegal” guys. […] When that meeting was over I held a game called IKARI WARRIORS in my hands which I had to crack till the next meeting to prove that I could really crack and to get accepted to join Frontline. Those guys let me know that the game had a pretty hard protection on it and that they doubt that I’d be able to do the crack anyway […].’ It is important to emphasize how the subcultural rite of passage was constructed through proficiency in technology use. After successful copy protection removal, ‘Weasel’ went with the copied game to the next meeting to attend a ceremony of joining the group: ‘DEEJAY was the only cracker in that group and he was also the one who had to “examine” my work if it was good or whatever. […] he said after looking into my work for a pretty long while: “Well, the crack isn’t bad at all! […] My decision is: Let him join!” That was the beginning of my long and still lasting scene-career as a cracker.’39
10![]()
This testimony shows clearly that technology-oriented subculture did not exist in a social vacuum. Hackers were not lone geeks for whom computers as the second self were a substitute for social relations. The episode is also an example of hacker jargon. Instead of the word hacker, the names illegal guys and sceners are used. Along with cracker, these terms were the most popular self-descriptions of computer underground members.
Another interview with a scener from Austria shows a typical pattern of evolution from computer end-user and gamester to cracker through participation in exchange networks of pirate programs: ‘First, I bought warez from local lamers […] then I decided to swap [i.e. exchange games] with local dudes, schoolmates etc. Some people I simply met at libraries, some at computer stores, that stuff. Finally I stumbled across local coders […] that gave me the kick to hunt for more decent people. This way, I stumbled over some TSK members, chatted them up, showed them what I can do and eventually became member… the rest is history…’40
The interviewee mentions a practice of copying games for money for schoolmates. This was very popular among adolescent computer users who wanted to earn money in addition to the pocket money from their parents. Those who copied games for money are described here as lamers, a derogative term adopted from the urban slang term lame – in opposition to cool. According to an insider, this term was adopted specifically from skateboard slang.41
11![]()
The lamers were those who tried to exist in the computer scene but did not uphold the appropriate etiquette and cultural values. The quoted interviewee describes his schoolmates as lamers because they broke the rule that cracked games should be distributed on a non-profit basis, which was one of the crucial distinctions between the commercial and the cracked software distribution systems.42 A lamer was also someone who tried to exist within the subculture, not just the ordinary gamester who merely copied pirate games. According to computer underground values, three categories of computer users exist: real sceners, often called elite, lamers, described with derogative terms, and gamesters, mostly presented as neutral. This distinction is similar to the social structure of clubbers. Thornton describes a strict distinction between hips, hipsters and squares.43 Hip means someone who is capable of upholding the whole value system established by a specific subculture, or even introduces an innovation; a hipster is someone who is trying to dress and behave like a hip, but lacks skills to be accepted by the hip community. A square is an outsider without affection toward the subculture.
The distribution of pirate games was closely linked to the creation of amateur graphics and music. In an interview, the two founders of the Genesis Project, a well-known German group established in Aachen, describe such activities: ‘i got a c-64 around 1984 and used to play a lot of those funny 1982-games […]. half a year later i […] started to draw pictures with that brandnew “koalapainter” [graphics editing tool]! then i got bored of doing everything on my own. so i asked my best friends “the nasty ounk” (tno) and catman if they would like to make a little group of computer-artists.’44
‘They were classmates of mine. Ounk was a great artist, while Catman knew a lot of guys who always got the latest games in our city. Soon everyone at our school was talking about “those cool G*P disks”, which always contained the latest games and awesome graffiti-like artwork by Ounk on the disk-covers. After a while our disks were passed on to kids at other schools. And soon every C64 user in the city of Aachen, Germany had heard of Genesis*Project. A lot of kids wanted to join G*P, but I wanted to keep the group as small as possible. I only wanted people in the group who had a special skill or genuine talent.’45 Adding high-quality and well-designed logos and graphics was highly regarded among this community. These memories show that members of the scene saw themselves as computer artists who were not only distributing computer games but also sharing their pieces of ingenious graphics and design included in modified games and on paper covers of 5,25” disks.46
12![]()
It is important to focus on the handles as well as on group names and zine titles. Frequently, such names referred to the illegality of the cracking scene. For instance, two of the most popular early zines were named Illegal: Raubkopierer Magazin and Sex’n’Crime. However, names that parodied the computer industry, such as German Cracking Service or International Cracking Company, were also popular.47 Another favored feature of chosen names was references to youth culture. The editor of Illegal had the handle Jeff Smart, the hero of the popular comic series Clever & Smart. References to Star Wars and The Lord of The Rings as well as other favorite TV series and movies of the 1980s were also frequent among sceners.48 Some references were quite obscure, and their understanding required extended knowledge of the context of the youth culture of the era. For instance, the popular group Fairlight had the name of the synthesizer used by Depeche Mode and Jean Michel Jarre – favorite musicians of the group’s founders.49
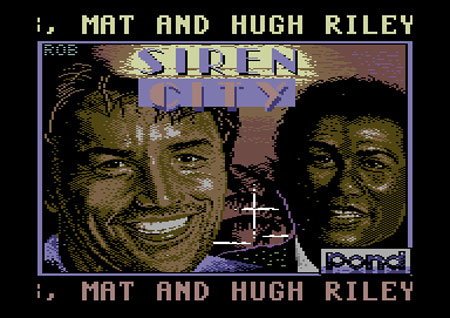
References to popular culture were frequently present in the graphics and music created by amateur computer artists. Quite often, their compositions were covers of popular electronic music of the 1980s, which were composed by programming the C-64 sound chip. With 57 covers, the most popular music theme among them was definitely Harold Faltermeyer’s Axel F – Beverly Hills Cop music theme. Jan Hammer’s Crockett’s Theme from the Miami Vice soundtrack was also popular (22 covers), and music themes from Terminator (20), Star Wars (16) and Blade Runner (9) were also covered. Popular culture topics were common themes in computer graphics. The most frequent were computer versions of Boris Vallejo and Frank Frazetta’s fantasy paintings full of dragons and half-naked sorceresses repainted manually pixel by pixel. Pictures of favorite series and movie heroes were also popular, for instance the original logo and lead actors of Miami Vice.
Front page of Miami Vice Demo, 1987. The parody of the well-known computer game developer Ocean in the lower right corner is worth noting. The word ‘pond’ is written with the original font used in the company logo. Such parodies of computer industry names were popular among diverse groups of computer users.
(http://noname.c64.org/csdb/release/?id=13768)
Moreover, contemporary scene zines are sources that provide knowledge on the lifestyles and interests of German, Dutch or Swedish adolescents.
– what are your favourites?
+ good videos, applejuice, nice demos, girls, music from ‘mike oldfield’ and ‘sisters of mercy’. and soon: riding in my very own ‘golf gti’!!
[…]
– what kind of a person are you?
+ i’m neither a popper nor a punk. i wear a normal outfit, but i think black ! i love new wave and acid. […]
– what do you do the rest of your life?
+ […] maybe iam going to study on the university in aachen. or i’ll become a computer-specialist on tv […]. i am also reading a lot of books. my fave author is ‘stephen king’.50
In a zine interview, another German shared his taste in the 1980s action movies: ‘ALIENS, PLATOON, RAMBO 1, RAMBO 2, RAMBO 3, RAMBO 4, RAMBO 5.’51
13![]()
Numerous popular culture references pointed out in this chapter show how adolescent computer users were impacted by the media culture of the era. In literature on the subcultures of the 1980s, authors focus on the formation of masculinity through rituals of independence from mainstream society, for instance by listening to indie rock.52 The case of the cracking scene shows a different and more complex picture of youth. A cracker could be interested in doing something supposedly illegal while at the same time shaping his identity with a nick from Star Wars or The Lord of the Rings; and his creative activity, besides cracking games, would encompass covering the Miami Vice soundtrack. Moreover, crackers openly admitted their interest in the practices of consumption such as going to parties, buying expensive consumer electronics or driving a Golf GTI, one of the most iconic cars of youth car culture. Teenagers also mixed different forms of culture, for instance listening to Sisters of Mercy while being interested in acid and rave scenes. Those two music genres are traditionally discussed as significant for completely different subcultures, in this case goths and clubbers.
Similar testimonies, in which crackers claim their cultural interests, can be found in sources concerning the cracking scene in most Northwestern European countries. The testimonies of crackers from various countries are strikingly similar, especially those concerning their lifestyles and social activities. On the one hand, it is possible that adolescents from West Germany, Sweden and the Netherlands of the 1980s actually had a similar lifestyle. As scene maga-zines were written in English for audiences from other countries, on the other hand it is possible that crackers simply wanted to present themselves as Europeans by referring to cultural practices and icons which could be recognized abroad while intentionally not discussing their national cultures.
3. The Rise and Fall of the International Illegal Scene
According to a narrative popular among insiders of the European computer underground, the whole subculture was started in 1983 by a few young hobby programmers from West Germany. These young crackers founded two groups: JEDI and German Cracking Service. It is difficult to estimate the actual impact of these two groups on the growth of the whole subculture. The computer underground linked with C-64 is documented by The C-64 Scene Database (CSDB) – an online software archive platform and forum with a sophisticated search engine. According to data retrieved from CSDB, in 1983-84 the scene grew rapidly and simultaneously in several countries, not only in West Germany. The growth of the scene continued throughout 1985 to reach its peak in 1988, when it slowly began to decline. Visualizations of the statistical data from online databases by Markku Reunanen show the growth and further decline of the C-64 scene.53 In the second half of the 1980s, the computer underground was to be found in most Northwestern European countries. During that time, a well-organized transnational system of distributing pirate software and zines was established in West Germany, the UK, the Netherlands, Denmark, Sweden and Norway.54
14![]()
At the beginning, groups encompassed peers from mostly the same city. It was primarily a reproduction of pre-existing social networks within the framework of computer culture. Later, groups started to grow in terms of numbers of members and evolved into remoter structures which communicated via telephone calls and correspondence. Most of the groups encompassed members from the same country; however, during the peak of the scene, some international groups were established.
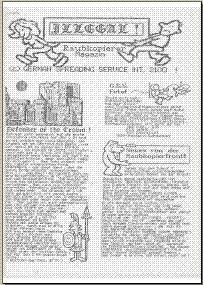
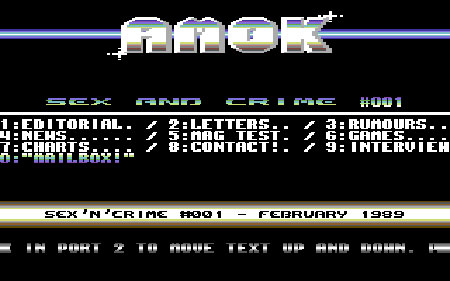
Aside from spreading pirate software, computer underground created probably the biggest homogenous zine culture in Europe. The phenomenon of zines – homemade magazines distributed through personal networks and mailing lists – has its roots in American science-fiction fan culture and counterculture of the 1960s.55 At the beginning, members of the computer scene published paper magazines and distributed them in a small number of photocopies among friends and correspondence contacts. Typical computer underground zines included some news from the scene, interviews with respected crackers, discussions of current scene topics, lists of top ten games based on readers’ votes, reports from parties and game reviews. Articles on programming were scarce since due to constant competition, sceners were not eager to share their technical knowledge. Topics not related to computers, such as reviews of popular movies and music records, were also included. The first paper zines were the German Illegal (1986-89) and the British Iguana (1988-89). Paper zines were subsequently replaced by digital zines, so called diskmags – executable files on disks that included essays presented in graphic layout and with music. The first digital zine, Sex’n’Crime (1989-90), was published in Germany.56
Cover of Illegal 18 (1989)
(http://noname.c64.org/csdb/release/index.php?id=39720)
Front page of Sex’n’Crime digital zine, 1989
(http://noname.c64.org/csdb/release/?id=8825)
The zines aimed to create a common media platform for sceners on which they could express their opinions and find information about the activities of other groups. Authors emphasized the fact that computer zine culture distributed information alternative to available commercial computer magazines, such as the English Computer and Video Games, ZZap64! or the German 64’er, which were accused of being dependent on the software industry. Game reviews and top ten games lists in zines were presented as content written by independent gamesters and crackers.57
15![]()
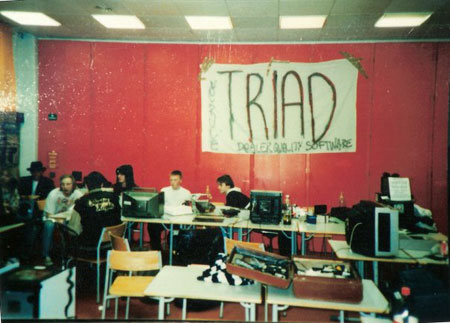
Members of the scene were eager to meet other sceners in person. One of the possibilities was to attend computer fairs, such as ‘Personal Computer World’ in London. It was customary for crackers to hang around together at the venue, to look at available software novelties that were to be cracked soon and to make pranks. The second possibility of meeting others was a so-called copy party. It was a weekend event organized by a scene group in a rented school or culture center. Participants traveled to copy parties with hardware that was plugged in to copy new software as well as to play games together. During the party, numerous contests were held, for instance for best graphics, music and the results of live cracking. These gatherings were attended exclusively by adolescent males and commonly featured heavy drinking, pranks and vandalism.
Attendees of a copy party (early 1990s); note the slogan: ‘Dealer Quality Software’
(http://www.atlantis-prophecy.org/recollection/?load=photos&sub=pic&id=288&page=0)
Information about such parties could only be attained through personal contacts, thus only people from a specific circle attended.58 One of the first copy parties was the ‘Plutonium Party’ organized in West Berlin in the summer of 1984 by the Plutonium Crackers.59 A reminiscence of this party shows an atmosphere of secretiveness, a common feature of the early copy parties that were supposed to be illegal: ‘The exact meeting place was not announced beforehand, not because of illegality issues, but just because it was cool, James Bond style. Cracking didn’t have that illegal touch of today, it was rather a Robin-Hood-esque elegant tricking of the system.’60
During the early period of the scene, parties took place without any police interference. However, during the late 1980s the police started to raid parties in West Germany and confiscated all pirate software – and also hardware. Due to the constant danger of police raids, the most popular and biggest copy party was held in the Netherlands where, according to sceners, software piracy was not prosecuted yet. This party, named ‘Venlo Meeting’, was organized in the small Dutch town of Venlo and took place every few months from December 1987 until April 1994 (58 editions). At the peak of its popularity there were more than one thousand attendees. Such big copy parties, of course, could not be held in secrecy anymore.
16![]()
Attendees of Venlo Meeting, 1990
(http://www.atlantis-prophecy.org/recollection/?load=photos&sub=pic&id=306&page=0)
The rise of the international cracking scene in the second half of the 1980s was also the beginning of its end. Mass software piracy was increasingly condemned in computer magazines as well as in mainstream media. Not only hackers who broke into computer networks, but also small-scale software pirates started to be perceived as an issue of media moral panic. For example, the German lawyer Günter von Gravenreuth started a private crusade against crackers and became the symbol of anti-piracy campaigns of the era. Aside from publicizing the threat software pirates posed, he directly provoked crackers by forging numerous copies of an alleged letter from Tanja, a young girl who was interested in the exchange of software. He sent these letters to crackers, whose addresses were easy to find in pirate software. However, the result of this action is not clear.61 The issue of piracy became one of the hot spots in debates of computerization in West Germany. In December 1988, Highscore, a computer game program on WDR television, organized and broadcasted a discussion between Gravenreuth and well-known German crackers.62 Highscore also presented a report from a RadWar copy party as well as material on crackers with alleged live cracking.63
Around the turn of the 1980s and 1990s, with increasing frequency the police in West Germany, Denmark, Sweden and France organized raids on private homes of alleged crackers, confiscated all hardware and imposed fines. As a result, crackers changed their tactics. Software was now distributed only among trusted friends and crack intros no longer featured private addresses and telephone numbers.64 Further changes in the international pirate scene were linked to the introduction of the Internet. In the late 1990s, members of the Internet warez scene used password-protected File Transfer Protocol servers and later peer to peer protocols to distribute pirate software.
Some crackers now focused on adding visual and audio effects instead of cracking games. They started to produce demos, a jargon name for demonstration programs. Instead of cracking software, members of this subculture were interested in making multimedia presentations that explored the boundaries of hardware capabilities as well as presenting the artistic talents of programmers.65 In the early 1990s, the demoscene, also called legal scene, replaced the cracking scene as the most popular computer-oriented subculture. This subculture, which later adopted PC platforms, still exists. There are numerous demoscene gatherings; the biggest of them is the ‘Breakpoint’, organized annually in Germany.
17![]()
In the early 1990s, adolescents who had shaped the beginning of the computer underground had simply grown older. From the memories and testimonies written by retired crackers, one can conclude how easily they used their subcultural capital in subsequent job careers. Frequently, crackers attended polytechnic universities – primarily, to no surprise, computer sciences. After entering the job market they usually found decent jobs as programmers and IT consultants. In the early 1990s, due to their expert knowledge on modifying structures of computer games as well as creating innovative digital graphics and music, computer game companies welcomed crackers. Their specific approach to computer aesthetics significantly influenced computer games for the Commodore Amiga, the successor of the C-64 and dominant home computer platform in that era. Some innovative European game companies such as Team 17 (Worms) and Core Design (Tomb Raider) were even masterminded by former crackers. Those experienced in computer graphics and music were later frequently employed in the cultural industries in general, thus significantly impacting digital graphics and electronic music of the 1990s and 2000s.
The aim of my article was to discuss the features and dynamics of the first mass computer-oriented subculture, which was established by home computer users long before the introduction of the Internet. The establishment of computer underground was a side effect of the enormous popularity of home computers, which became one of the symbols of the 1980s along with hair-spray hairstyles, New Romantic music and graphic violence movies. The development of this subculture was linked to growing numbers of adolescent users who evolved from gamesters to crackers. Being an illegal guy who cracked and distributed recently released computer games was certainly an attractive identity for a male adolescent growing up in Europe during the 1980s. However, the rapid growth of the subculture decreased its attractiveness, and being a cracker in the 1990s no longer meant that one belonged to an elite computer avant-garde. On the other hand, this cultural phenomenon turned into an issue of media moral panic in the second half of the 1980s, which sparked the interest of law enforcement agencies in young software pirates. Paradoxically, in the early 1990s being a cracker became too dangerous and at the same time less attractive than a few years earlier.
Some aspects of computer underground have already been discussed in literature. However, the fact that this specific culture was significantly influenced not only by contemporary technology, but by the social and cultural contexts of the era, is not yet adequately recognized. Young hackers were teenagers interested in the outside world, not only in computer monitors, as Levy and Turkle argued. What is more, the activities of the illegal scene were a part of the male youth’s struggle for masculinity similar to an interest in heavy metal music or cars.66 Male adolescents adopted the C-64 as an artifact that could be used in creating social prestige within the peer group and masculinity based on technical expertise. The course of computer use was far different from the visions of computer education programs promoted by the prophets of the information society. Only a few years later, however, with their expert knowledge these adolescents contributed to the development of computer industries in Europe as programmers and IT consultants.
18![]()
In the current discourse of hacktivism (i.e. socially engaged hacking), all historical practices of computer undergrounds are interpreted as an intentional engagement aiming for social change. The case discussed here clearly shows that the cultural practices of the first mass computer-oriented subculture had nothing to do with political and social engagement. The development of milieus of computer hackers interested in social change had rather different trajectories; it began with actions by the American group Cult of the Dead Cow and with the editors of 2600: The Hacker Quarterly in the mid-1980s.67 Those circles played a significant role as advocates of consumer electronics by publicizing information about the practices of powerful American telecommunication companies as well as hardware and software manufacturers. The case of the cracking scene also shows the huge difference between the practices of cracking and the open source movement. A cracked computer game was a commodity used in a gift economy system shared by computer users. No one was eager to share their know-how on cracking with other groups, which were actually competitors. When studying contemporary trends such as the free software movement we have to be careful: instead of accepting the claims of social actors such as the famous slogan ‘information wants to be free’, we should rather learn more about the struggle for prestige and social capital in the high-tech world.
I have also discussed a few similarities with the graffiti scene and club culture to show how the growth of computer underground fits into the general history of youth culture. I focused on showing how adolescent crackers referred to the material world in which they lived. Aside from sitting in front of computer monitors, they also dreamed of owning a Golf GTI, hung around in local skate parks or met at fast food restaurants. On the other hand, youth hackers lived in popular culture fantasies. If we want to study the history of the information society, besides such figures as Bill Gates, Steve Wozniak and, in the case of Germany, Heinz Nixdorf, we need to include such prominent figures as John Rambo, Axel Foley and Sonny Crockett. Home computers, VCR and cable TV are currently recognized primarily as symbols of 1980s nostalgia. Future academic studies on the side effects of the domestication of these media technologies can contribute to our understanding of the social and cultural dynamics of the 1980s and 1990s – decades that are only recently being discovered by historians.
1 Frank Webster, Theories of Information Society, London 2006.
2 Educational software for children became popular in the 1980s. See: Mizuko Ito, Engineering Play. A Cultural History of Children’s Software, Cambridge 2009.
3 Jane Wheelock, Personal Computing, Gender and an Institutional Model of the Household, in: Roger Silverstone/Eric Hirsch (eds), Consuming Technologies. Media and Information in Domestic Spaces, London 1992, Reprint 2005, pp. 89-103, here pp. 94-95. See also James Sumner’s contribution to this issue.
4 One of the most interesting, though rather overlooked monographs on the dangers of information technologies is: Theodore Roszak, The Cult of Information, Berkeley 1986. The most popular book on hackers, which also played a significant role in the dissemination of hacker culture, is: Steven Levy, Hackers. Heroes of the Computer Revolution, Garden City 1984. See also: Douglas Thomas, Hacker Culture, Minneapolis 2003.
5 Kenneth Thompson, Moral Panics, London 1998. For moral panic about youth and subcultures, see: Stanley Cohen, Folk Devils and Moral Panics, London 1980.
6 Levy’s book (fn. 4) not only had great impact on the popularization of the American hacker culture. It also influenced the popular picture of the lone computer geek, who is unable to interact with other people, especially women.
7 Sherry Turkle, The Second Self. Computers and the Human Spirit, Cambridge 2005.
8 David Bell, An Introduction to Cybercultures, London 2002; Steven G. Jones (ed.), Virtual Culture. Identity and Communication in Cybersociety, London 2002; Howard Rheingold, The Virtual Community, London 2000.
9 The BBS technology, portrayed in the movie War Games, was widely spread in the US since the early 1980s. Despite its huge popularity, it is remembered exclusively by insiders, see: http://www.textfiles.com.
10 I have discussed the comparison between European and American computer users in a conference presentation: Patryk Wasiak, Hacking across the Atlantic: How Young Hackers ‘Phreaked’ Transatlantic Telephone Cables. Part of the Soft-EU Panel: Geographies of Computing. Straddling the Divide between the Global and the Local. Society for the History of Technology, Annual Meeting, Cleveland, 4 November 2011.
11 E.g. Martin Klimke/Joachim Scharloth (eds), 1968 in Europe. A History of Protest and Activism, 1956–1977, New York 2008.
12 Stuart Hall/Tony Jefferson (eds), Resistance Through Rituals. Youth Subcultures in Post-War Britain, London 2003; Dick Hebdige, Subculture. The Meaning of Style, London 1979.
13 Ken Gelder/Sarah Thornton (eds), The Subcultures Reader, London 1997; David Muggleton/Rupert Weinzierl (eds), The Post-Subcultures Reader, Oxford 2003; Ken Gelder, Subcultures. Cultural Histories and Social Practice, London 2007.
14 Leslie Haddon, Explaining ICT Consumption. The Case of the Home Computer, in: Silverstone/Hirsch, Consuming Technologies (fn. 3), pp. 75-88, here p. 82.
15 ‘Newscopy’ (pseudonym), SCENETOWN. A Crash Course in Scene-Evolution, URL: http://www.atlantis-prophecy.org/recollection/?load=online_issues&issue=0&sub=article&id=2.
16 Sherry Turkle, The Second Self (fn. 7).
17 David Muggleton, Inside Subculture. The Postmodern Meaning of Style, Oxford 2000.
18 Due to the lack of specific regulations and police interest, computer piracy was not fought by the police in Western Europe and the US until the very late 1980s.
19 The introduction of copy protection systems in the software company Sierra On Line was described by Levy, Hackers (fn. 4), pp. 389-406.
20 Nancy Macdonald, The Graffiti Subculture. Youth, Masculinity and Identity in London and New York, Houndmills 2002. The American graffiti scene was documented well by Martha Cooper/Henry Chalfant, Subway Art, London 1984.
21 Sarah Thornton, Club Cultures. Music, Media and Subcultural Capital, Cambridge 2010.
22 Levy, Hackers (fn. 4), p. 391.
23 Graham Murdock/Paul Hartmann/Peggy Gray, Contextualizing Home Computing, in: Silverstone/Hirsch, Consuming Technologies (fn. 3), pp. 136-151, here p. 144.
24 A huge collection of often amusing and naïve news on the hacker peril was gathered by computer science experts in ‘The Risks Digest’ newsletter (since 1985): http://catless.ncl.ac.uk/Risks.
25 The social impact of War Games was analyzed by Thomas, Hacker Culture (fn. 4).
26 Haddon, Explaining ICT Consumption (fn. 14), p. 80.
27 Levy, Hackers (fn. 4), pp. 389-401.
28 Such signatures were already included in pirate Apple II games, see: http://www.textfiles.com/artscene/intros/APPLEII/. Sometimes the word cracked was intentionally misspelled as kracked. This was the characteristic hacker lingo adopted by computer-oriented communities, see: The Jargon File, URL: http://www.catb.org/jargon/html/index.html.
29 ‘Weasel’, the good ol’ dayz, in: Brainfart. The pARTy-zine 12 (1996), p. 7, URL: ftp://ftp.padua.org/pub/c64/Magazines/mags.c64.org/mags/B/brainfart06.zip.
30 This system was described in depth by Jukka Vuorinen, Ethical Codes in the Digital World. Comparisons of the Proprietary, the Open/Free and the Cracker System, in: Ethics and Information Technology 9 (2007), pp. 27-38.
31 Such an informal pirate media distribution system existed earlier among audio- and videophiles. Tape cassettes with bootleg concert records and video movies were exchanged on a non-profit basis with the help of classified advertisements. See: Joshua M. Greenberg, From BetaMax to Blockbuster. Video Stores and the Invention of Movies on Video, London 2008.
32 ‘Jeff Smart’, THE STATE OF BEING A CRACKER, in: Illegal 26 (1988), URL: http://www.triad.se/wp-content/uploads/2011/07/illeg26.txt.
33 For a general discussion on contemporary practices of shaping masculinity, see e.g.: Maurice Berger/Brian Wallis/Simon Watson (eds), Constructing Masculinity, London 1995. The historical junction between modern technology use and masculinity is discussed in: Ruth Oldenziel, Making Technology Masculine. Men, Women, and Modern Machines in America, 1870–1945, Amsterdam 2004.
34 Thornton, Club Cultures (fn. 21).
35 http://noname.c64.org/csdb/.
36 The emergence of the Polish cracking scene is discussed in: Patryk Wasiak, Playing and Copying: Social Practices of Home Computer Users in Poland during the 1980s, in: Gerard Alberts/Ruth Oldenziel (eds), European Hacker Cultures, Amsterdam 2012 (forthcoming); Patryk Wasiak, The East is Coming! The Demoscene in Eastern Europe, in: Rhizome, 21 May 2010, URL: http://rhizome.org/editorial/2010/may/21/the-east-is-coming-the-demoscene-in-eastern-europe.
37 An anecdote shows how cheating linked gamesters and hackers. ‘Someone went to a hacker in a [computer] club and said “Excuse me, I heard you’re very good in programming. I can’t complete the 34th level of this game, because there is a red monster that always kills me. Can’t you do something and remove that monster?” The hacker shrugged his shoulders, disassembled the game and removed the obstacle. The gamer was happy he could complete the level and by the way, the term cheater was born by him.’ Tamas Polgár, The Brief History of the Computer Demoscene, Berlin 2008, p. 63.
38 Macdonald, The Graffiti Subculture (fn. 20), p. 112.
39 ‘Weasel’, the good ol’ dayz (fn. 29), pp. 8-9. In the title of the interview ‘z’ is used instead of ‘s’; this is a typical misspelling widely used by software pirates. Such a misspelling is also used in the widespread term warez – a jargon description of pirate software. In the Internet era, the term warez scene became a jargon name for pirate software exchange networks. See: The Jargon File (fn. 28).
40 Interview with ‘Antitrack’, URL: http://zakalwe.fi/~shd/texts/imr/c37antit.htm.
41 ‘King Fisher/TRIAD’, Best Of Times, URL: http://www.atlantis-prophecy.org/recollection/?load=online_issues&issue=0&sub=article&id=3. Here is an alternative history of the lamer (http://www.definitions.net/definition/lamer): ‘This term seems to have originated in the Commodore-64 scene in the mid-1980s. It was popularized among Amiga crackers of the mid-1980s by “Lamer Exterminator”, the most famous and feared Amiga virus ever, which gradually corrupted non-write-protected floppy disks with bad sectors. The bad sectors, when looked at, were overwritten with repetitions of the string “LAMER!”.’
42 Vuorinen, Ethical Codes (fn. 30).
43 Thornton, Club Cultures (fn. 21), pp. 98-104.
44 Interview with ‘tnt’, in: Sex’n’Crime 1 (1989), URL: http://c64mags.untergrund.net/wiki/index.php?title=Sex_n_Crime_01. The name Genesis Project is a reference to Star Trek.
45 Genesis*Project. A (Not So) Brief History by Antichrist, founder of G*P, URL: http://www.atlantis-prophecy.org/recollection/?load=online_issues&issue=0&sub=article&id=8.
46 For artistic aspects of computer underground activities see: Daniel Botz, Kunst, Code und Maschine. Die Ästhetik der Computer-Demoszene, Munich 2011. However, other monographs on computer art ignore those amateur computer graphics and music, for instance: Dominic McIver Lopes, A Philosophy of Computer Art, London 2010.
47 In the US scene, contrary to Europe, vulgar group names were quite common, for instance, FUCK: Fucked Up College Kids. An extended list of American scene names is available online: http://www.textfiles.com/magazines/DELIRIUM/delacr11.txt.
48 Here is the list of the selected handles with references to popular culture according to the CSDB: Luke Skywalker – 9, Yoda – 3, Han Solo – 5, Darth Vader – 3, R2D2 – 3, Jabba – 3, Gandalf – 9, Frodo – 5, Sauron – 4, Gollum – 3, Rambo – 12, Terminator – 19, Predator – 14, MacGyver – 2, Blade Runner – 5, Metallica – 5 (http://noname.c64.org/csdb). Information based on the use of CSDB search engine.
49 Interview of the Month: ‘Strider/Fairlight’, in: Illegal 28 (1988), URL: http://www.triad.se/wp-content/uploads/2011/07/illeg28.txt.
50 Interview with ‘tnt’ (fn. 44). He refers to the short-lived subculture of poppers, which was spread primarily in West Germany.
50 Interview with ‘tnt’ (fn. 44). He refers to the short-lived subculture of poppers, which was spread primarily in West Germany.
51 See fn. 49.
52 Matthew Bannister, White Boys, White Noise. Masculinities and 1980s Indie Guitar Rock, Aldershot 2006.
53 Pouet.net visualized, 2011, URL: http://www.kameli.net/marq/?p=595.
54 The high costs of sending a large amount of letters abroad were a continuous problem for the scene. One of the solutions was so called stamp cheating. Stamps were covered with transparent substances such as glue, which enabled the recycling of the stamp by the receiver.
55 Diverse American zine cultures have been analyzed by Stephen Duncombe, Notes from Underground. Zines and the Politics of Alternative Culture, Bloomington 2008.
56 In the mid-1990s, along with the wide dissemination of the Internet, diskmags were replaced with IRC channels and online magazines.
57 Duncombe describes a similar system of music records reviews in American zines, which claimed to be more objective than mainstream music magazines. Duncombe, Notes from Underground (fn. 55).
58 The idea of underground parties as opposed to public events such as computer fairs, where anyone could enter, is also a distinctive trait of the club culture, see: Thornton, Club Cultures (fn. 21).
59 The name, as members of this group claimed, was taken from the fascination with Kraftwerk’s album Radio-Activity (1975); see http://noname.c64.org/csdb/group/?id=2536.
60 ALiEN/AnTiTraX, Plutonium Crackers Party 1984 ‘Drink With Nuclear Guys’, in: PAiN 10/2005, URL: http://noname.c64.org/csdb/event/showreport.php?report_id=81.
61 http://widerstreit.de/Die+Tanja-Briefe.htm.
62 The footage was uploaded on YouTube by RadWar, a cracking group whose members were guests of the program: http://www.youtube.com/watch?v=UCxz-V-WYTI. RadWar was a reference to Radiological Warfare – a term adopted from the Cold War media discourse. In the description of the uploaded footage the circumstances of the Highscore recording are discussed. An English transcription of the debate was published in: Illegal 34 (1989), URL: http://noname.c64.org/csdb/release/?id=13801.
63 http://www.youtube.com/watch?v=gGw0xtVol2M, http://www.youtube.com/watch?v=Bq8ENS1LEhI.
64 One of the methods of ‘going underground’ was coding contact data in distributed software. Only another experienced cracker could disassemble the program code and find an address or phone number. Such methods were also used by elite crackers to avoid lamers.
65 See: Botz, Kunst, Code und Maschine (fn. 46).
66 In her study of an online space populated by programmers, Lori Kendall discusses this cultural phenomenon as ‘a form of masculinity that is convergent with computer culture, itself a masculine domain’. Lori Kendall, Hanging Out in the Virtual Pub. Masculinities and Relationships Online, Berkeley 2002, p. 73.